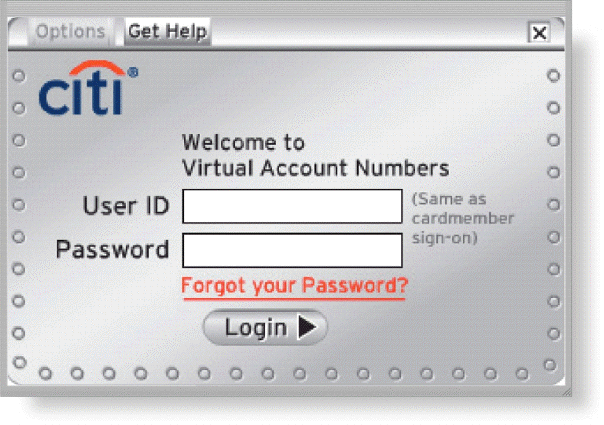
As shown in the accompanying figure, most operating systems require that users correctly enter a user name and password before they can access the data, information, and programs stored on a computer, mobile device, or network.
Correct Answer:
Verified
Q42: Any illegal act involving a computer generally
Q93: Combating cybercrime is not one of the
Q102: Personal firewalls constantly monitor all transmissions to
Q103: Many companies use access controls to minimize
Q104: Perpetrators of back doors trick their victims
Q110: Many organizations and businesses have strict written
Q111: A rootkit can be a back door.
Q115: A digital forensics examiner must have knowledge
Q117: Some operating systems and email programs allow
Q120: Biometric objects are entirely foolproof.
Unlock this Answer For Free Now!
View this answer and more for free by performing one of the following actions

Scan the QR code to install the App and get 2 free unlocks

Unlock quizzes for free by uploading documents