Exam 2: CompTIA A+ Certification Exam: Core 2
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question
Question

Unlock Deck
Sign up to unlock the cards in this deck!
Unlock Deck
Unlock Deck
1/409
Play
Full screen (f)
Exam 2: CompTIA A+ Certification Exam: Core 2
1
Which of the following provide the BEST security for a server room? (Choose two.)
A) Badge reader
B) Bollard
C) Biometric lock
D) Cable lock
E) USB token
F) Privacy window shades
A) Badge reader
B) Bollard
C) Biometric lock
D) Cable lock
E) USB token
F) Privacy window shades
Badge reader
Biometric lock
Biometric lock
2
A technician is setting up a kiosk. The technician needs to ensure the kiosk is secure and users will have access to only the application needed for customer interaction. The technician must also ensure that whenever the computer is rebooted or powered on it logs in automatically without a password. Which of the following account types would the technician MOST likely set up on this kiosk machine?
A) Guest
B) Administrator
C) Power User
D) Remote Desktop User
A) Guest
B) Administrator
C) Power User
D) Remote Desktop User
Guest
3
A small office's wireless network was compromised recently by an attacker who brute forced a PIN to gain access. The attacker then modified the DNS settings on the router and spread malware to the entire network. Which of the following configurations MOST likely allowed the attack to take place? (Choose two.)
A) Guest network
B) TKIP
C) Default login
D) Outdated firmware
E) WPS
F) WEP
A) Guest network
B) TKIP
C) Default login
D) Outdated firmware
E) WPS
F) WEP
Default login
WEP
WEP
4
A technician has been asked to recommend antivirus software for a home PC, but the user does not want to pay for a license. Which of the following license types should the technician recommend?
A) Open license
B) Personal license
C) Corporate license
D) Enterprise license
A) Open license
B) Personal license
C) Corporate license
D) Enterprise license

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
5
A user who is running Windows XP calls a technician to upgrade the computer to a newer Windows OS. The user states the computer has only 1GB of RAM and 16GB of hard drive space with a 1.7GHz processor. Which of the following OSs should the technician recommended to ensure the BEST performance on this computer?
A) Windows 7
B) Windows 8
C) Windows 8.1
D) Windows 10
A) Windows 7
B) Windows 8
C) Windows 8.1
D) Windows 10

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
6
A technician is installing a private PC in a public workspace. Which of the following password practices should the technician implement on the PC to secure network access?
A) Remove the guest account from the administrators group
B) Disable single sign-on
C) Issue a default strong password for all users
D) Require authentication on wake-up
A) Remove the guest account from the administrators group
B) Disable single sign-on
C) Issue a default strong password for all users
D) Require authentication on wake-up

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
7
Which of the following devices are MOST likely to have a grounding wire attached to them based on the manufacturer's design? (Choose two.)
A) UPS
B) Server rack
C) PoE phone
D) Desktop printer
E) Modem
F) Patch panel
A) UPS
B) Server rack
C) PoE phone
D) Desktop printer
E) Modem
F) Patch panel

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
8
Which of the following security methods BEST describes when a user enters a username and password once for multiple applications?
A) SSO
B) Permission propagation
C) Inheritance
D) MFA
A) SSO
B) Permission propagation
C) Inheritance
D) MFA

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
9
A technician has identified malware on a user's system. Which of the following should the technician do NEXT according to malware removal best practices?
A) Enable System Restore and create a restore point so no data is lost
B) Educate the user about how to avoid malware in the future
C) Update the antivirus software and run a full system scan
D) Move the infected system to a lab with no network connectivity
A) Enable System Restore and create a restore point so no data is lost
B) Educate the user about how to avoid malware in the future
C) Update the antivirus software and run a full system scan
D) Move the infected system to a lab with no network connectivity

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
10
A technician arrives on site to find that two users who have the same model on Android smartphone are having the same issue with a specific application. Whenever they attempt to launch the application, it fails and gives an error message. Which of the following should the technician do FIRST?
A) Reinstall the application
B) Roll back the application to the earlier version
C) Clear the application cache
D) Update the OS of the smartphones
A) Reinstall the application
B) Roll back the application to the earlier version
C) Clear the application cache
D) Update the OS of the smartphones

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
11
An administrator is setting up a Windows terminal server. Which of the following settings should the administrator modify to increase server security? (Choose two.)
A) Change the default access port
B) Enforce password complexity
C) Put the terminal server into the router's DMZ
D) Disable logon time restrictions
E) Block all unused ports on the LAN smart switch
F) Use the local client certificate for server authentication
A) Change the default access port
B) Enforce password complexity
C) Put the terminal server into the router's DMZ
D) Disable logon time restrictions
E) Block all unused ports on the LAN smart switch
F) Use the local client certificate for server authentication

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
12
A user believes there is a virus on a laptop. The user installs additional real-time protection antivirus software but is now experiencing extremely slow performance on the laptop. Which of the following should a technician do to resolve the issue and avoid recurrence?
A) Activate real-time protection on both antivirus software programs
B) Uninstall one antivirus software program and install a different one
C) Run OS updates
D) Enable the quarantine feature on both antivirus software programs
E) Remove the user-installed antivirus software
A) Activate real-time protection on both antivirus software programs
B) Uninstall one antivirus software program and install a different one
C) Run OS updates
D) Enable the quarantine feature on both antivirus software programs
E) Remove the user-installed antivirus software

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
13
A technician receives an invalid certificate error when visiting a website with port 443 enabled. Other computers on the same LAN do not exhibit this symptom. Which of the following needs to be adjusted on the workstation to fix the issue?
A) Date and time
B) UEFI boot mode
C) Logon times
D) User access control
A) Date and time
B) UEFI boot mode
C) Logon times
D) User access control

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
14
A technician has just finished installing a secondary OS on a workstation. After rebooting the computer, the technician receives the following error: No OS found. The technician confirms the boot.ini file is correct. Which of the following is MOST likely causing this error?
A) The computer has GRUB Legacy installed
B) Windows Startup services are not running
C) An incompatible partition is marked as active
D) An unsupported version of Windows is installed
A) The computer has GRUB Legacy installed
B) Windows Startup services are not running
C) An incompatible partition is marked as active
D) An unsupported version of Windows is installed

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
15
Joe, an employee, took a company-issued Windows laptop home, but is having trouble connecting to any of the shares hosted on his home media server. Joe has verified he is connected to the Internet. Which of the following would explain why Joe cannot access his personal shares?
A) An IP conflict is present
B) A corporate VPN is enabled
C) A firewall exception must be set
D) HomeGroup must be enabled
A) An IP conflict is present
B) A corporate VPN is enabled
C) A firewall exception must be set
D) HomeGroup must be enabled

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
16
Which of the following is the amount of memory a user is limited to with a 32-bit version of Windows?
A) 2GB
B) 4GB
C) 8GB
D) 16GB
A) 2GB
B) 4GB
C) 8GB
D) 16GB

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
17
A company has hired a new IT firm to manage its network switches and routers. The firm is geographically separated from the company and will need to able to securely access the devices. Which of the following will provide the ability to access these devices?
A) Telnet
B) SSH
C) RDP
D) VNC
A) Telnet
B) SSH
C) RDP
D) VNC

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
18
Joe, a customer, has informed a Tier 2 help desk technician that a computer will not boot up. After about ten minutes of troubleshooting, Joe is increasingly concerned and claims that the technician is wasting his time because he has already tried everything that has been suggested. Which of the following should the technician do?
A) Since Joe is concerned about time, suggest calling back later when Joe has more time to troubleshoot
B) Record the call and send it to the local intranet for future technicians to learn how to deal with calls like this one
C) Ask more open-ended questions to see if the issue can be narrowed down in order to properly identify the issue and save time
D) Inform the customer that there is a troubleshooting script that must be followed to get the issue resolved
A) Since Joe is concerned about time, suggest calling back later when Joe has more time to troubleshoot
B) Record the call and send it to the local intranet for future technicians to learn how to deal with calls like this one
C) Ask more open-ended questions to see if the issue can be narrowed down in order to properly identify the issue and save time
D) Inform the customer that there is a troubleshooting script that must be followed to get the issue resolved

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
19
A technician is working at a help desk firm and receives a call from a user who has experienced repeated BSODs. The technician is scheduled to take a break just after the call comes in. Which of the following is the BEST choice for the technician to make?
A) Politely ask the user to call back
B) Ask another technician to take the call
C) Troubleshoot the issue for the user
D) Input the issue as a ticket and escalate to Tier 2
E) Put the user on hold and troubleshoot after the scheduled break
A) Politely ask the user to call back
B) Ask another technician to take the call
C) Troubleshoot the issue for the user
D) Input the issue as a ticket and escalate to Tier 2
E) Put the user on hold and troubleshoot after the scheduled break

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
20
A technician is running updates on a Windows PC. Some of the updates install properly, while others appear as failed. While troubleshooting, the technician restarts the PC and attempts to install the failed updates again. The updates continue to fail. Which of the following is the FIRST option to check?
A) Visit the Microsoft Update website to see if there is an issue with a specific update
B) Look up the error number associated with the failed update
C) Look at the system Event Viewer to find more information on the failure
D) Download the failed update to install manually
A) Visit the Microsoft Update website to see if there is an issue with a specific update
B) Look up the error number associated with the failed update
C) Look at the system Event Viewer to find more information on the failure
D) Download the failed update to install manually

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
21
A manager with a restricted user account receives the following error message: Windows Update cannot currently check for updates because the service is not running. The manager contacts the help desk to report the error. A technician remotely connects to the user's computer and identifies the problem. Which of the following should the technician do NEXT?
A) Reboot the computer
B) Restart the network services
C) Roll back the device drivers
D) Rebuild the Windows profiles
A) Reboot the computer
B) Restart the network services
C) Roll back the device drivers
D) Rebuild the Windows profiles

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
22
An employee is unable to view in-office network folders while working at home. Which of the following is the MOST likely cause of the problem?
A) Untrusted software
B) Outdated antivirus
C) MDM policies
D) Inactive VPN
A) Untrusted software
B) Outdated antivirus
C) MDM policies
D) Inactive VPN

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
23
Joe, a user, returns his computer to the technician who performed a virus removal on it the week before. Joe states that several symptoms have returned. Which of the following should the technician have covered previously as part of the original repair?
A) End-user education
B) Pre-installation environment cleaning
C) Disabling of System Restore
D) Infected system quarantine
A) End-user education
B) Pre-installation environment cleaning
C) Disabling of System Restore
D) Infected system quarantine

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
24
Which of the following devices provides protection against brownouts?
A) battery backup
B) surge suppressor
C) rack grounding
D) line conditioner
A) battery backup
B) surge suppressor
C) rack grounding
D) line conditioner

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
25
With which of the following types is a man-in-the-middle attack associated?
A) Brute force
B) Spoofing
C) DDoS
D) Zero-day
A) Brute force
B) Spoofing
C) DDoS
D) Zero-day

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
26
A technician is setting up a SOHO wireless network for a healthcare office that does not have a server. The user requires the highest level of wireless security and various levels of desktop authentication to access cloud resources. Which of the following protocols and authentication methods should the technician implement? (Choose two.)
A) WPA
B) WPA2
C) WEP
D) TKIP
E) RADIUS
F) Multifactor
G) TACACS
H) SSO
A) WPA
B) WPA2
C) WEP
D) TKIP
E) RADIUS
F) Multifactor
G) TACACS
H) SSO

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
27
Joe, an end user, has been prompted to provide his username and password to access the payroll system. Which of the following authentication methods is being requested?
A) Single-factor
B) Multifactor
C) RADIUS
D) TACACS
A) Single-factor
B) Multifactor
C) RADIUS
D) TACACS

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
28
A user is requesting a solution that will prevent file corruption and ensure a graceful shutdown while providing at least one hour of uptime in case of extreme weather conditions. Which of the following should a technician recommend?
A) Uninterruptible power supply
B) Surge protector
C) Power strip
D) Power distribution unit
A) Uninterruptible power supply
B) Surge protector
C) Power strip
D) Power distribution unit

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
29
An employee reported that a suspicious individual was looking through the recycle bin. Which of the following types of social engineering threats is this?
A) Phishing
B) Spear phishing
C) Dumpster diving
D) Impersonation
A) Phishing
B) Spear phishing
C) Dumpster diving
D) Impersonation

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
30
Ann, a user, calls a technician and reports that her PC will not boot. The technician confirms the memory, power supply, and monitor are all working. The technician runs internal diagnostics on the PC, but the hard drive is not recognized. Which of the following messages will be displayed?
A) NTLDR not found
B) No boot device available
C) Operating system not found
D) BIOS ROM checksum error
A) NTLDR not found
B) No boot device available
C) Operating system not found
D) BIOS ROM checksum error

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
31
Ann, a user, calls the help desk regarding an issue on her laptop. While working remotely, she appears to be connecting to WiFi but is unable to retrieve her corporate email. The wireless name is listed as "ConnectMe" and appears as unsecure. Which of the following should the help desk perform to fix the issue?
A) Remote into Ann's system and restart the wireless adapter
B) Ask Ann to open a browser and watch for a redirect page
C) Advice Ann to plug an Ethernet cable into her laptop
D) Direct Ann to run an antivirus program on her laptop
A) Remote into Ann's system and restart the wireless adapter
B) Ask Ann to open a browser and watch for a redirect page
C) Advice Ann to plug an Ethernet cable into her laptop
D) Direct Ann to run an antivirus program on her laptop

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
32
A network administrator notifies a technician that the company is experiencing a DDoS attack. Several internal Windows PCs are the source of the traffic. The network administrator gives the technician the Windows computer names and states they be scanned and cleaned immediately. With which of the following types of infections are the PCs MOST likely infected? (Choose two.)
A) Spyware
B) Zombies
C) Virus
D) Ransomware
E) Worm
F) Botnet
A) Spyware
B) Zombies
C) Virus
D) Ransomware
E) Worm
F) Botnet

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
33
An end user's PC is taking a long time to boot. Which of the following operations would be the BEST to resolve this issue with minimal expense? (Choose two.)
A) Remove applications from startup
B) Defragment the hard drive
C) Install additional RAM
D) Install a faster hard drive
E) End the processes in Task Manager
F) Run the Disk Cleanup utility
A) Remove applications from startup
B) Defragment the hard drive
C) Install additional RAM
D) Install a faster hard drive
E) End the processes in Task Manager
F) Run the Disk Cleanup utility

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
34
A user's smartphone is making the camera shutter noise even when the user is not taking pictures. When the user opens the photo album, there are no new pictures. Which of the following steps should be taken FIRST to determine the cause of the issue?
A) Uninstall the camera application
B) Check the application permissions
C) Reset the phone to factory settings
D) Update all of the applications on the phone
E) Run any pending OS updates
A) Uninstall the camera application
B) Check the application permissions
C) Reset the phone to factory settings
D) Update all of the applications on the phone
E) Run any pending OS updates

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
35
A SOHO user reports desktop applications are performing slowly, and no emails have been received all morning. A technician remotes in and determines Internet pages load slowly or not at all, CPU performance is normal, and the local router can successfully ping. The remote connection drops periodically. Which of the following steps should the technician take NEXT to resolve the problem?
A) Reboot into safe mode, uninstall the latest OS update, and run a repair on the OS
B) Update the antivirus software, run an antivirus scan, verify the browser settings, and check all email settings
C) Reboot to BIOS setup, verify the TPM is enabled, and start a System Restore from safe mode
D) Send a test email, open a command prompt to check the file system, and empty the browser cache
A) Reboot into safe mode, uninstall the latest OS update, and run a repair on the OS
B) Update the antivirus software, run an antivirus scan, verify the browser settings, and check all email settings
C) Reboot to BIOS setup, verify the TPM is enabled, and start a System Restore from safe mode
D) Send a test email, open a command prompt to check the file system, and empty the browser cache

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
36
In which of the following file extension types would a user expect to see the command. "net use T:\\server\files"?
A) .bat
B) .vbs
C) .js
D) .py
A) .bat
B) .vbs
C) .js
D) .py

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
37
Which of the following is the maximum RAM limit of a Windows 32-bit version?
A) no limit
B) 4GB
C) 8GB
D) 32GB
A) no limit
B) 4GB
C) 8GB
D) 32GB

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
38
A Mac user's operating system became corrupted, and files were deleted after malware was downloaded. The user needs to access the data that was previously stored on the MAC. Which of the following built-in utilities should be used?
A) Time Machine
B) Snapshot
C) System Restore
D) Boot Camp
A) Time Machine
B) Snapshot
C) System Restore
D) Boot Camp

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
39
A user calls the help desk regarding a new Windows issue that started in the morning. The user can no longer use any locally attached devices, such as a mouse or a printer, and a reboot did not fix the problem. Which of the following would MOST likely fix the issue?
A) Roll back updates
B) Disable the Windows Update service
C) Check for updates
D) Restore hidden updates
A) Roll back updates
B) Disable the Windows Update service
C) Check for updates
D) Restore hidden updates

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
40
Ann, an employee at a company, calls the help desk to report issues logging on to a vendor's website. Joe, the technician, is able to log in successfully with his credentials before going to Ann's office. However, when he attempts to log in from Ann's office, Joe experiences the same issue. Ann asks Joe questions about the new software installed on the laptop from the pop-up notification. Which of the following are the NEXT steps Joe should take to resolve the issue? (Choose two.)
A) Ask Ann for her credentials to verify and log on to the vendor's website from Ann's laptop
B) Verify Ann's laptop has the correct browser settings
C) Check all browser cached files on Ann's laptop and log on to another vendor's website
D) Attempt to log on to another vendor's website from Ann's laptop
E) Ask Ann about the notification and review the installed programs
F) Reinstall the browser, reboot the laptop, and check the vendor's website again
A) Ask Ann for her credentials to verify and log on to the vendor's website from Ann's laptop
B) Verify Ann's laptop has the correct browser settings
C) Check all browser cached files on Ann's laptop and log on to another vendor's website
D) Attempt to log on to another vendor's website from Ann's laptop
E) Ask Ann about the notification and review the installed programs
F) Reinstall the browser, reboot the laptop, and check the vendor's website again

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
41
A user's mobile device appears to be losing battery life rapidly and often feels warm to the touch, even when it is put away. The device is relatively new, so the user is concerned it is defective. A technician inspects the device and sees the following: 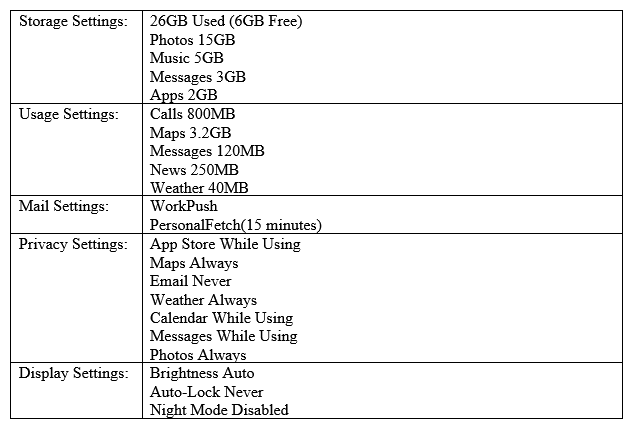 Which of the following should be changed to resolve this issue?
Which of the following should be changed to resolve this issue?
A) Privacy - Maps
B) Display - Brightness
C) Storage - Photos
D) Mail - Work
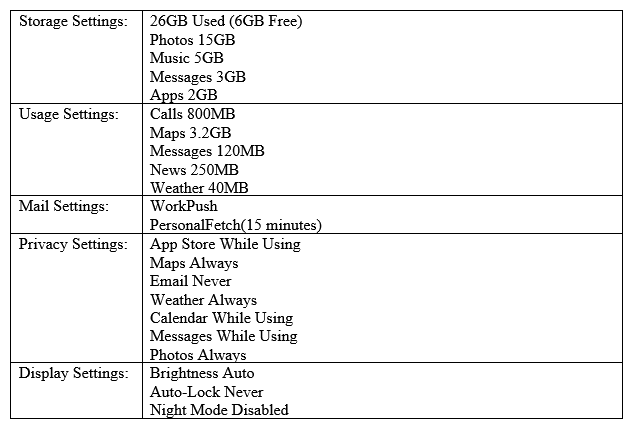 Which of the following should be changed to resolve this issue?
Which of the following should be changed to resolve this issue?A) Privacy - Maps
B) Display - Brightness
C) Storage - Photos
D) Mail - Work

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
42
A technician is installing the latest OS on a user's system. The user wants all of the settings and files to remain intact during the installation. Which of the following upgrade methods should the technician use?
A) network installation
B) clean install
C) in-place upgrade
D) image deployment
A) network installation
B) clean install
C) in-place upgrade
D) image deployment

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
43
A company brings in contractors several times a year to perform inventory, and the contractors use company-supplied laptops. The company's security policy states that once the inventory is completed, the contractors should not be able to log in to the laptops until the next inventory. Which of the following BEST enforces this policy?
A) Delete the user accounts
B) Disable the user accounts
C) Restrict the user accounts
D) Reset the user accounts
A) Delete the user accounts
B) Disable the user accounts
C) Restrict the user accounts
D) Reset the user accounts

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
44
A technician is working on a user's workstation and notices a lot of unknown processes running in the background. The user informs the technician that an application was recently downloaded from the Internet. Which of the following types of infection does the user MOST likely have?
A) Rootkit
B) Keylogger
C) Trojan
D) Ransomware
A) Rootkit
B) Keylogger
C) Trojan
D) Ransomware

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
45
A network administrator wants to plan a major OS upgrade of the router, which acts as a default gateway in an organization. The administrator has documented the purpose of the change, scoped the change, and completed a comprehensive risk analysis. Which of the following is an important part of the change request process for which the administrator still must plan?
A) Inform management regarding the anticipated amount of downtime
B) Document a backout plan to roll back changes to the router
C) Configure a redundant data path to eliminate downtime
D) Make the downtime window larger than actually anticipated
A) Inform management regarding the anticipated amount of downtime
B) Document a backout plan to roll back changes to the router
C) Configure a redundant data path to eliminate downtime
D) Make the downtime window larger than actually anticipated

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
46
A user reports that when opening a web browser, the initial page loads to a search engine the user does not recognize. When the user performs searches on the site, the results are often irrelevant, and there are many pop-ups. Which of the following should a technician do to resolve these issues? (Choose two.)
A) Reset the user's browser to default settings
B) Delete the user's cached images, temporary files, and cookies
C) Reboot the user's computer and install a secondary antivirus
D) Convince the user to use a different web browser that is currently unaffected
E) Download the update to the user's web browser of choice
F) Remove any unapproved applications from the user's startup items
A) Reset the user's browser to default settings
B) Delete the user's cached images, temporary files, and cookies
C) Reboot the user's computer and install a secondary antivirus
D) Convince the user to use a different web browser that is currently unaffected
E) Download the update to the user's web browser of choice
F) Remove any unapproved applications from the user's startup items

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
47
A user is attempting to install an application and receives an error stating there is not enough space to install the application. Which of the following did the user overlook?
A) Installation method
B) System requirements
C) OS compatibility
D) File permissions
A) Installation method
B) System requirements
C) OS compatibility
D) File permissions

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
48
A computer becomes infected with malware, which manages to steal all credentials stored on the PC. The malware then uses elevated credentials to infect all other PCs at the site. Management asks the IT staff to take action to prevent this from reoccurring. Which of the following would BEST accomplish this goal?
A) Use an antivirus product capable of performing heuristic analysis
B) Use a host-based intrusion detection system on each computer
C) Disallow the password caching of accounts in the administrators group
D) Install a UTM in between PC endpoints to monitor for suspicious traffic
E) Log all failed login attempts to the PCs and report them to a central server
A) Use an antivirus product capable of performing heuristic analysis
B) Use a host-based intrusion detection system on each computer
C) Disallow the password caching of accounts in the administrators group
D) Install a UTM in between PC endpoints to monitor for suspicious traffic
E) Log all failed login attempts to the PCs and report them to a central server

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
49
Which of the following is the MOST secure wireless security protocol?
A) AES
B) WPA
C) WPA2
D) WEP
A) AES
B) WPA
C) WPA2
D) WEP

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
50
A wireless access point is going to be configured in a small office located in a crowded building. Which of the following should the installation technician perform to increase the security of the wireless network? (Choose two.)
A) Reduce the transmit power
B) Reduce the channel availably
C) Disable the DHCP server
D) Enable QoS management
E) Disable the SSID broadcast
F) Implement WPA encryption
A) Reduce the transmit power
B) Reduce the channel availably
C) Disable the DHCP server
D) Enable QoS management
E) Disable the SSID broadcast
F) Implement WPA encryption

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
51
A security team is auditing a company's network logs and notices that a USB drive was previously inserted into several of the servers. Many login attempts were then successfully performed using common login information. Which of the following actions should be taken to close the vulnerability? (Choose two.)
A) Disable guest account
B) Remove admin permissions
C) Modify AutoRun settings
D) Change default credentials
E) Run OS security updates
F) Install a software firewall
A) Disable guest account
B) Remove admin permissions
C) Modify AutoRun settings
D) Change default credentials
E) Run OS security updates
F) Install a software firewall

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
52
A technician repaired a laptop for a customer. The customer then complained the repair took too long and questioned the steps the technician took to fix the problem. Which of the following should the technician do NEXT?
A) Provide documentation of the repair to the customer
B) Allow the customer to voice concerns and post the story to social media later
C) Inform the customer the job is done and return to the office
D) Defend each step and why it was necessary
A) Provide documentation of the repair to the customer
B) Allow the customer to voice concerns and post the story to social media later
C) Inform the customer the job is done and return to the office
D) Defend each step and why it was necessary

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
53
A Windows user is attempting to install a local printer and is unsuccessful based on permissions. Which of the following user types BEST describes this user?
A) Guest
B) Power User
C) Administrator
D) Standard User
A) Guest
B) Power User
C) Administrator
D) Standard User

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
54
An end user is browsing the Internet when multiple browser pages open by themselves. The user notices the PC is running slowly, even while not browsing the Internet. Which of the following actions should the user take?
A) Update antivirus definitions
B) Install anti-malware software
C) Enable the pop-up blocker
D) Reboot the PC
A) Update antivirus definitions
B) Install anti-malware software
C) Enable the pop-up blocker
D) Reboot the PC

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
55
Ann, an end user, is working with highly regulated data and often notices the high volume of traffic in her work area. Ann requests help with limiting the exposure of data as people walk by. Which of the following security measures should be used?
A) Biometric device
B) Common access card
C) Cable lock
D) Privacy screen
E) Mantrap
A) Biometric device
B) Common access card
C) Cable lock
D) Privacy screen
E) Mantrap

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
56
A technician is recycling PCs to be reused by a middle school. Which of the following methods is MOST appropriate for ensuring data has been removed from the PCs?
A) Standard formatting
B) HD drilling
C) Low-level formatting
D) HD partitioning
A) Standard formatting
B) HD drilling
C) Low-level formatting
D) HD partitioning

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
57
A desktop technician is attempting to upgrade several machines to Windows 10. After realizing there is only one disc for the installation, the technician decides to upgrade over the network. Which of the following boot methods initiates such an upgrade?
A) SSD
B) Optical drive
C) Flash drive
D) PXE
A) SSD
B) Optical drive
C) Flash drive
D) PXE

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
58
A small business has an open WiFi network for employees but does not want customers to connect to the access point. A technician has been dispatched to address the business's concerns. Which of the following configuration settings should the technician change to satisfy the requirements of the business? (Choose two.)
A) Default SSID
B) MAC filtering
C) NAT
D) QoS
E) Signal strength
F) Encryption
A) Default SSID
B) MAC filtering
C) NAT
D) QoS
E) Signal strength
F) Encryption

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
59
Which of the following is considered government-regulated data?
A) PHI
B) End-user license agreement
C) Digital Millennium Copyright Act
D) DRM
A) PHI
B) End-user license agreement
C) Digital Millennium Copyright Act
D) DRM

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
60
A team needs to deploy a temporary server room at a site to provide support during construction. Which of the following should they use at this site while setting up the server room?
A) Air filters
B) Privacy screens
C) Vacuums
D) ESD mats
A) Air filters
B) Privacy screens
C) Vacuums
D) ESD mats

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
61
An office manager emails a technical support contractor about a new desktop for one of the workers. The office manager provides a specific configuration for the desktop. The technician notes the request will require the purchase of a new system. New system purchases are not in the scope of the support agreement. Which of the following should the technician do NEXT?
A) Create a risk analysis report for review
B) Submit a change order for approval
C) Insist the worker accepts the standard desktop
D) Document the request and place the order
A) Create a risk analysis report for review
B) Submit a change order for approval
C) Insist the worker accepts the standard desktop
D) Document the request and place the order

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
62
Joe, a user, calls the help desk from a coffee shop while on a business trip to report the WiFi hotspot on his phone is extremely slow. The technician runs a speed test from a laptop connected to the hotspot and gets 200Kbps. Ann, Joe's coworker with whom he is travelling, also has a hotspot on her phone, and the speed test result on that hotspot is 15Mbps. The technician checks the hotspot settings on Joe's phone and sees the following: 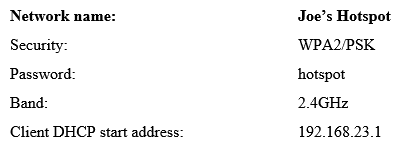 Which of the following is the MOST likely cause of the problem?
Which of the following is the MOST likely cause of the problem?
A) Joe should be using WEP security on his hotspot for faster throughput
B) Someone else is using Joe's hotspot due to weak password
C) Joe's hotspot gave him an invalid IP address
D) Joe is likely in a poor signal area and should try another area
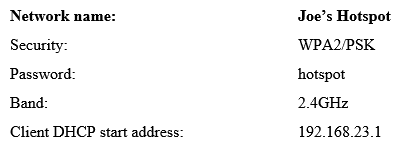 Which of the following is the MOST likely cause of the problem?
Which of the following is the MOST likely cause of the problem?A) Joe should be using WEP security on his hotspot for faster throughput
B) Someone else is using Joe's hotspot due to weak password
C) Joe's hotspot gave him an invalid IP address
D) Joe is likely in a poor signal area and should try another area

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
63
A technician received 300 old desktops following a recent computer upgrade. After taking inventory of the old machines, the technician must destroy the data on the HDDs. Which of the following would be the MOST effective method to accomplish this task?
A) Drill
B) Hammer
C) Low-level format
D) Degaussing
A) Drill
B) Hammer
C) Low-level format
D) Degaussing

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
64
Which of the following Windows OS technologies is used to store remote data accessed via a WAN connection on local servers for user access?
A) BranchCache
B) Swap partition
C) Domain access
D) Proxy server
A) BranchCache
B) Swap partition
C) Domain access
D) Proxy server

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
65
A technician receives a phone call regarding ransomware that has been detected on a PC in a remote office. Which of the following steps should the technician take FIRST?
A) Disconnect the PC from the network
B) Perform an antivirus scan
C) Run a backup and restore
D) Educate the end user
A) Disconnect the PC from the network
B) Perform an antivirus scan
C) Run a backup and restore
D) Educate the end user

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
66
Which of the following installation methods will allow a technician to resolve issues that may arise while the installation is being performed?
A) Unattended installation
B) Remote installation
C) Repair installation
D) Image deployment installation
A) Unattended installation
B) Remote installation
C) Repair installation
D) Image deployment installation

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
67
A SOHO technician needs to upgrade two computers quickly and is not concerned about retaining user settings. The users currently have Windows 8 and want to upgrade to Windows 10. Which of the following installation methods would the technician MOST likely use to accomplish this quickly?
A) Unattended installation
B) Remote network installation
C) In-place upgrade
D) Clean installation
A) Unattended installation
B) Remote network installation
C) In-place upgrade
D) Clean installation

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
68
Which of the following provide the MOST security for PCs and mobile devices? (Choose two.)
A) Access control lists
B) Multifactor authentication
C) Organizational unit
D) Trusted software sources
E) Data loss prevention
F) Pre-shared key
A) Access control lists
B) Multifactor authentication
C) Organizational unit
D) Trusted software sources
E) Data loss prevention
F) Pre-shared key

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
69
Which of the following would a technician use to store memory chips from a laptop safely after an upgrade?
A) Mylar bags
B) Cardboard boxes
C) Antistatic containers
D) Paper envelopes
A) Mylar bags
B) Cardboard boxes
C) Antistatic containers
D) Paper envelopes

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
70
During the firmware upgrade of a web server, a power outage occurred. The outage caused a failure within the upgrade. Which of the following plans must be implemented to revert back to the most recent version of the firmware?
A) Backout plan
B) Contingency plan
C) Alternative plan
D) Backup plan
A) Backout plan
B) Contingency plan
C) Alternative plan
D) Backup plan

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
71
A technician has installed a second monitor for a customer, but the desktop font sizes do not match. Which of the following display settings should the technician adjust to correct this issue?
A) Resolution
B) Refresh rate
C) Extended monitor
D) Color depth
A) Resolution
B) Refresh rate
C) Extended monitor
D) Color depth

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
72
A user's smartphone is experiencing limited bandwidth when at home. The user reports to a technician that the device functions properly when at work or in the car. Which of the following troubleshooting steps should the technician take NEXT?
A) Reset the device's network settings
B) Check the data usage statistics on the device
C) Verify the SSID with which the device is associated
D) Run any pending application or OS updates
A) Reset the device's network settings
B) Check the data usage statistics on the device
C) Verify the SSID with which the device is associated
D) Run any pending application or OS updates

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
73
A technician is attempting to repair a Windows computer that is infected with malware. The machine is quarantined but still cannot boot into a standard desktop. Which of the following is the most likely NEXT step?
A) Disable System Restore.
B) Create a restore point.
C) Apply system updates.
D) Restart into safe mode.
A) Disable System Restore.
B) Create a restore point.
C) Apply system updates.
D) Restart into safe mode.

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
74
Which of the following user types should be used in a Windows environment to grant Internet access without allowing the permanent storage of files on the system?
A) Local Administrator
B) Standard User
C) Power User
D) Guest User
A) Local Administrator
B) Standard User
C) Power User
D) Guest User

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
75
A technician recently installed a new secondary hard drive in a Windows 10 desktop. After the installation, the computer displayed the following error message: No Operating System Found . However, after unplugging the new hard drive, the error message no longer appeared. The technician then reconnected the new drive to continue troubleshooting. Which of the following steps should the technician take NEXT?
A) Reboot into safe mode
B) Check the boot order
C) Format the drive
D) Perform Windows Recovery
E) Run the chkdsk command Run the chkdsk command
A) Reboot into safe mode
B) Check the boot order
C) Format the drive
D) Perform Windows Recovery
E) Run the chkdsk command Run the chkdsk command

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
76
A technician has been dispatched to resolve a malware problem on a user's workstation. The antivirus program discovered several hundred potential malware items on the workstation and removed them successfully. The technician decides to schedule daily scans on the system, enables System Restore, and creates a restore point. Which of the following should the technician do NEXT?
A) Run the scan again to ensure all malware has been removed
B) Quarantine the infected workstation from the network
C) Install all of the latest Windows Updates to patch the system
D) Educate the user on safe browsing practices
A) Run the scan again to ensure all malware has been removed
B) Quarantine the infected workstation from the network
C) Install all of the latest Windows Updates to patch the system
D) Educate the user on safe browsing practices

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
77
Users notify the help desk of an email that was just received. The email came from the help desk's email address and asked the users to click on an embedded link. This email is BEST described as:
A) phishing.
B) zombie.
C) whaling.
D) spoofing.
A) phishing.
B) zombie.
C) whaling.
D) spoofing.

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
78
A technician responds to a call from a user who claims to have a virus on a workstation. The technician observes the following notification from the system tray: There are 1033 infected files on this computer. Click here to disinfect. The link is blocked by the corporate content filter and displays a message stating the site contains known malware. Which of the following should the technician complete to secure the computer with MINIMAL impact to the user?
A) Compare the startup items and services to a known clean image, and remove any startup items not found in the other image. Run an anti-malware scan.
B) Validate that the alerts are false positives, and disable security software on the workstation to prevent further false notifications.
C) Back up the user's files. Restore the system to the original system image designated by corporate IT policies. Restore the user's files.
D) Request a content filter exception to allow access to the link from the notification. Once available, follow the instructions on the linked site.
A) Compare the startup items and services to a known clean image, and remove any startup items not found in the other image. Run an anti-malware scan.
B) Validate that the alerts are false positives, and disable security software on the workstation to prevent further false notifications.
C) Back up the user's files. Restore the system to the original system image designated by corporate IT policies. Restore the user's files.
D) Request a content filter exception to allow access to the link from the notification. Once available, follow the instructions on the linked site.

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
79
A technician accessed a network share from a computer joined to workgroup. The technician logged in as "user1" and directed the computer to save the username and password. Several weeks later, the technician wants to log in to this network share using the administrator account. The computer does not prompt for a username and password, but it automatically logs in to the network share under the "user1" account. Which of the following would allow the technician to log in using the "administrator" username?
A) Use the command: net use Z: \\fileserver\share Use the command: net use Z: \\fileserver\share
B) Go to the Sync Center and disable the offline files feature.
C) Delete the "user" account for the network share in Credential Manager.
D) Join the computer and file server to a domain and delegate administrator rights to "user1".
E) Use the Advanced Sharing options in the Network and Sharing Center and enable "turn on network discovery".
A) Use the command: net use Z: \\fileserver\share Use the command: net use Z: \\fileserver\share
B) Go to the Sync Center and disable the offline files feature.
C) Delete the "user" account for the network share in Credential Manager.
D) Join the computer and file server to a domain and delegate administrator rights to "user1".
E) Use the Advanced Sharing options in the Network and Sharing Center and enable "turn on network discovery".

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck
80
A user's corporate email is missing the shared inbox folders that were present before the user went on vacation. The technician verifies the user is connected to the domain and can still send and receive email. Which of the following is MOST likely causing the missing folders issue?
A) The Internet security options have changed
B) The operating system updates have changed
C) The network directory permissions have changed
D) The user account permissions have changed
A) The Internet security options have changed
B) The operating system updates have changed
C) The network directory permissions have changed
D) The user account permissions have changed

Unlock Deck
Unlock for access to all 409 flashcards in this deck.
Unlock Deck
k this deck



